Security Features in Action
See how Elderlink's multi-layered security system protects users while maintaining accessibility
Click image to enlarge
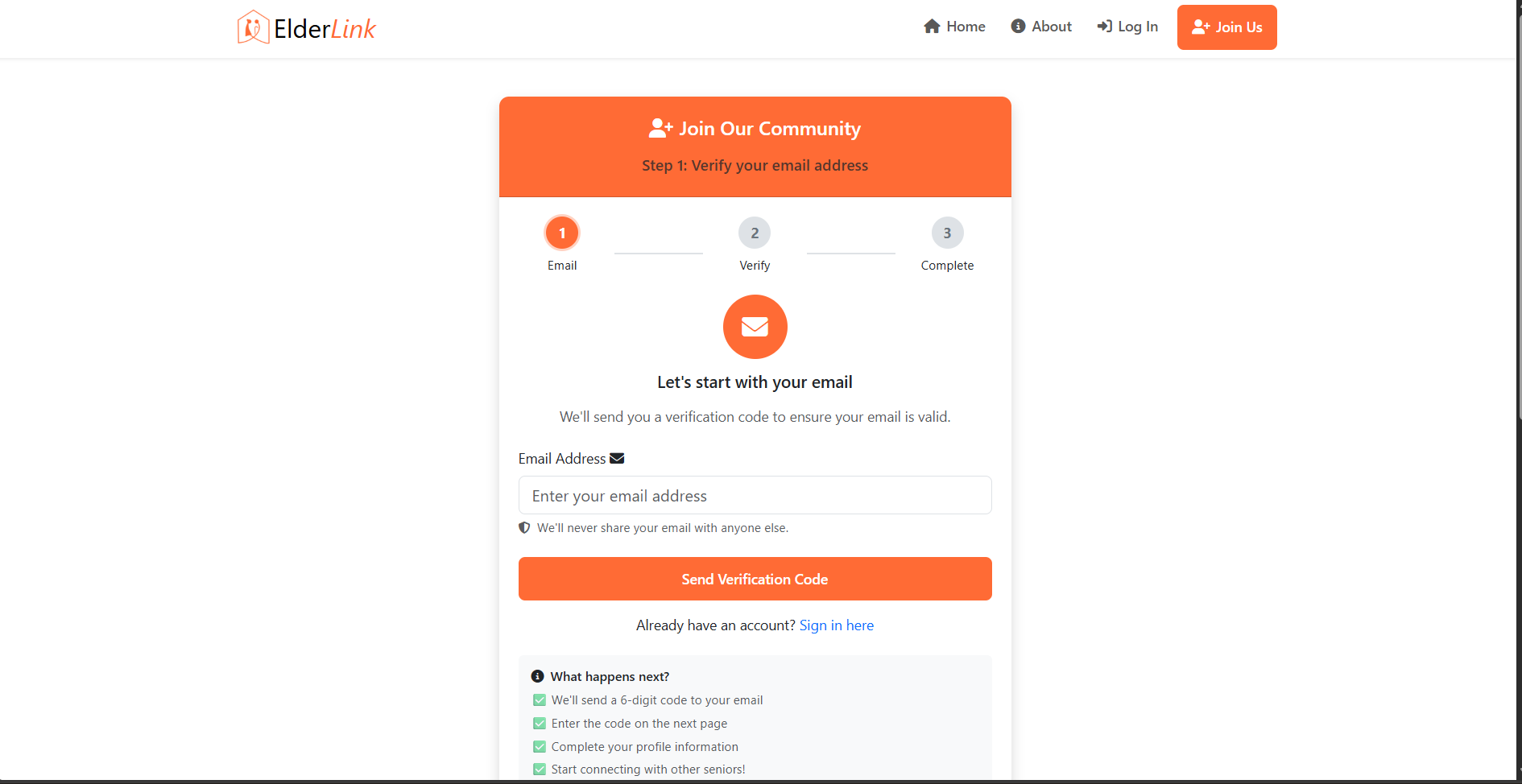
User Registration
Streamlined signup process with real-time password strength validation and clear form feedback
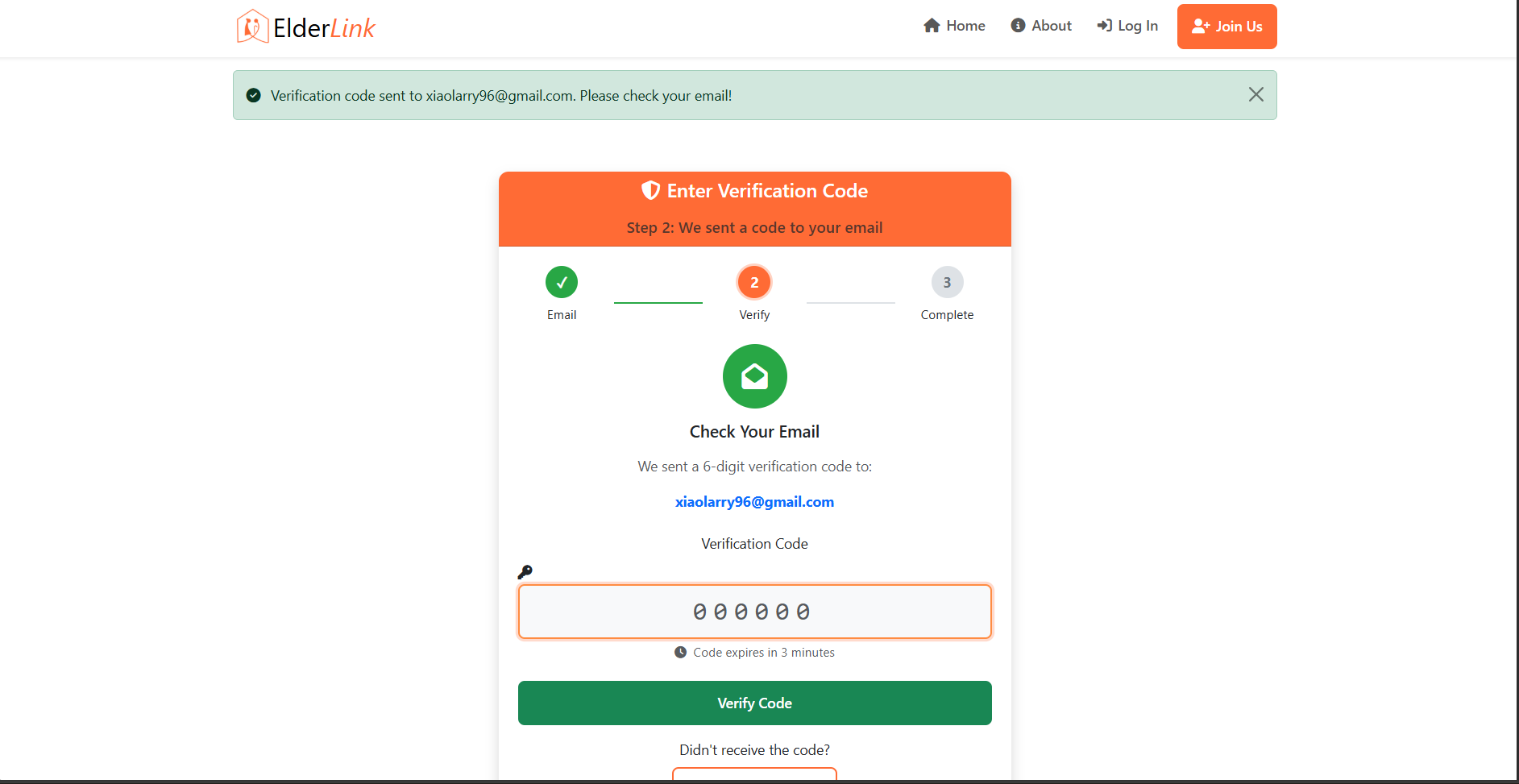
Email Verification System
Account activation via email confirmation ensuring verified user identities and valid contact information
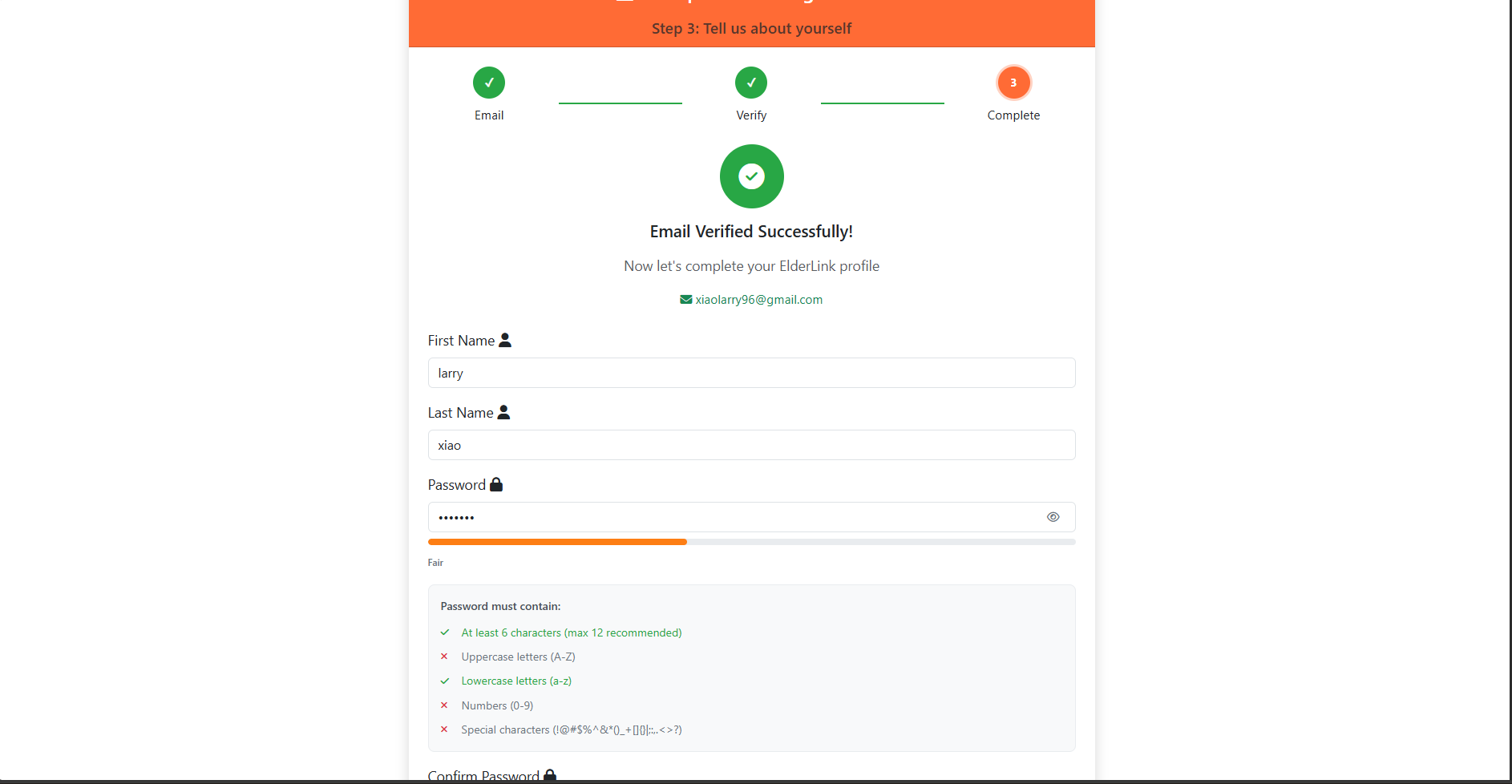
Registration Completion
Final step of the signup process confirming successful account creation and email verification status. This also ensures that user creates a strong password to match Elderlink's password policy
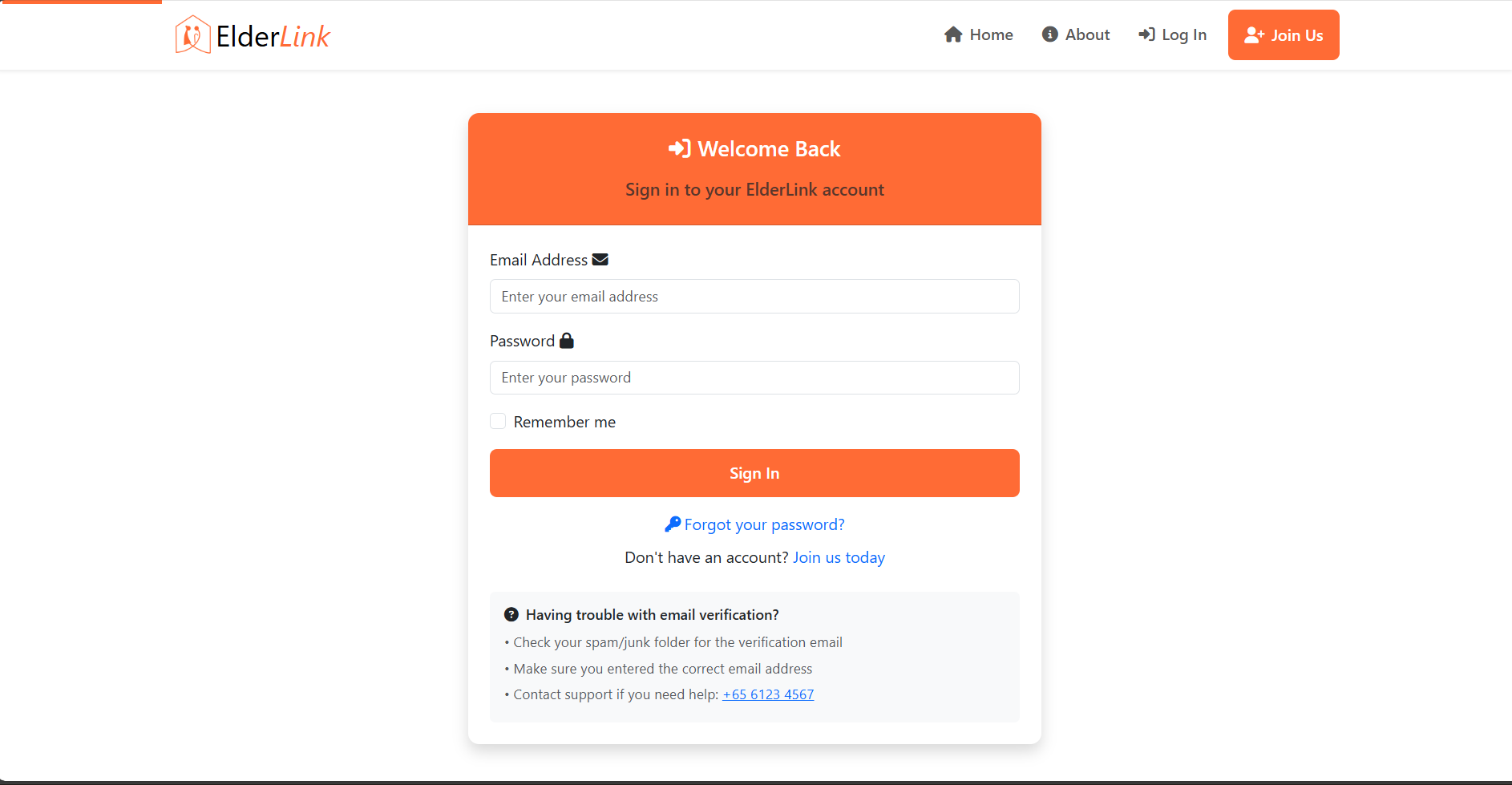
Secure Login Interface
Clean, accessible login form with clear error messages and user guidance designed for elderly users
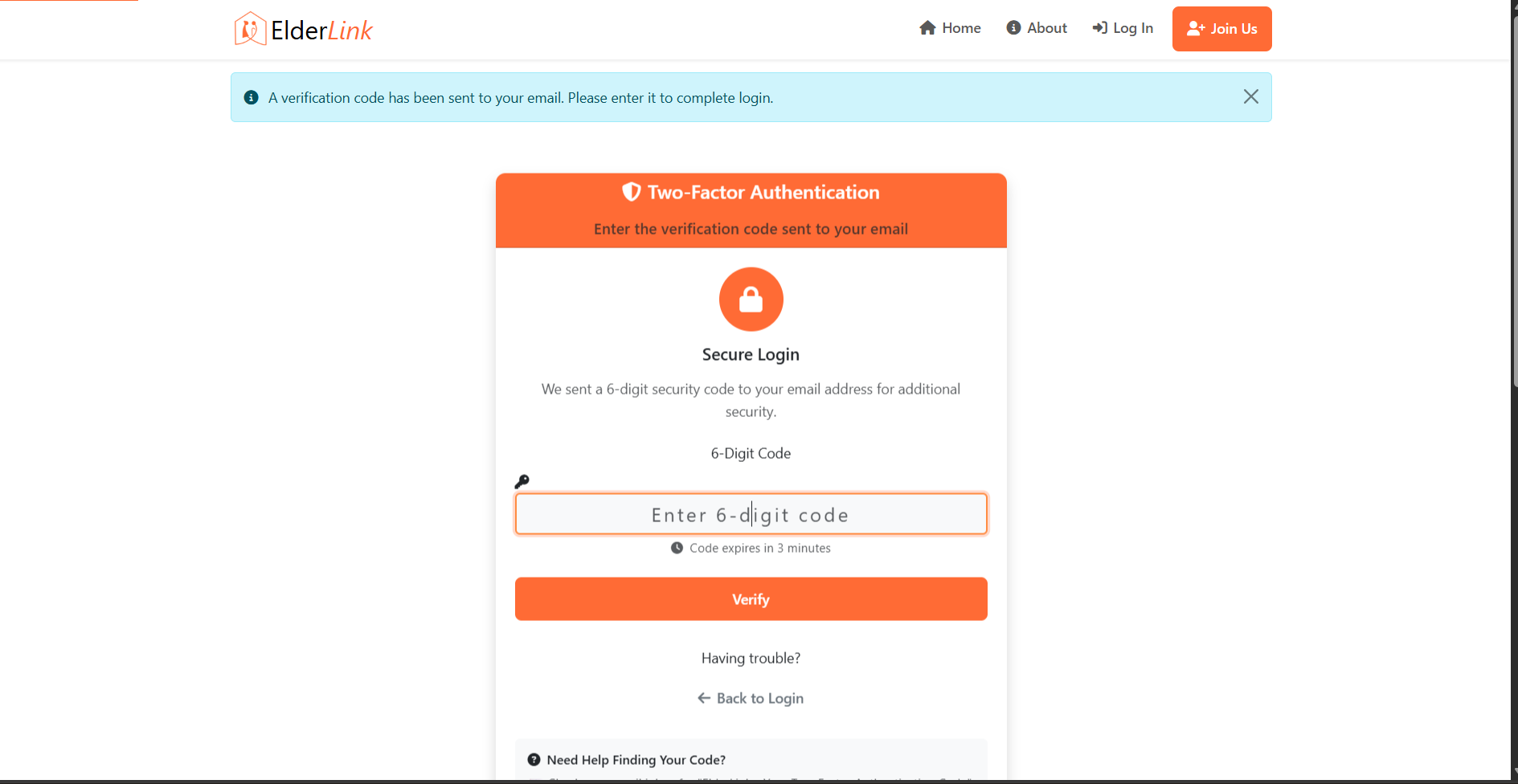
Two-Factor Authentication (2FA)
Additional security layer with email-based verification codes for enhanced account protection
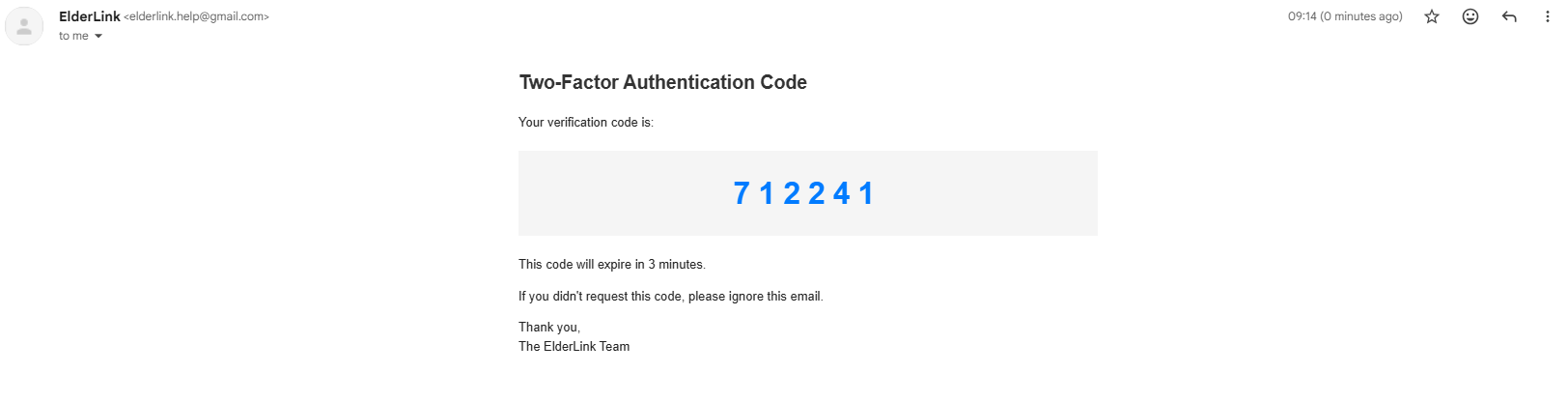
2FA Email Delivery
Automated email system sending time-sensitive verification codes for two-factor authentication
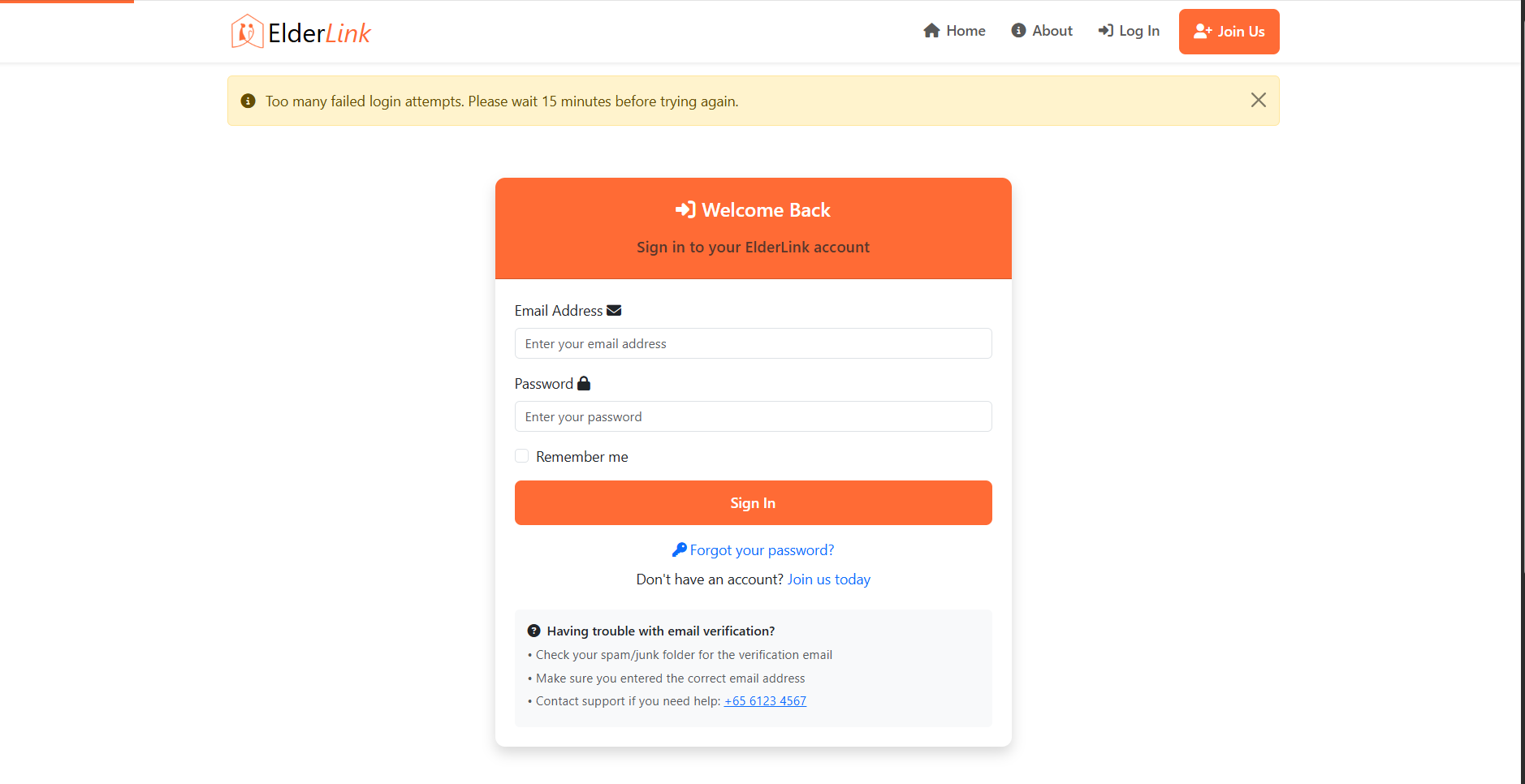
Rate Limiting & Brute-Force Protection
Intelligent throttling system limiting login attempts to prevent automated attacks and credential stuffing
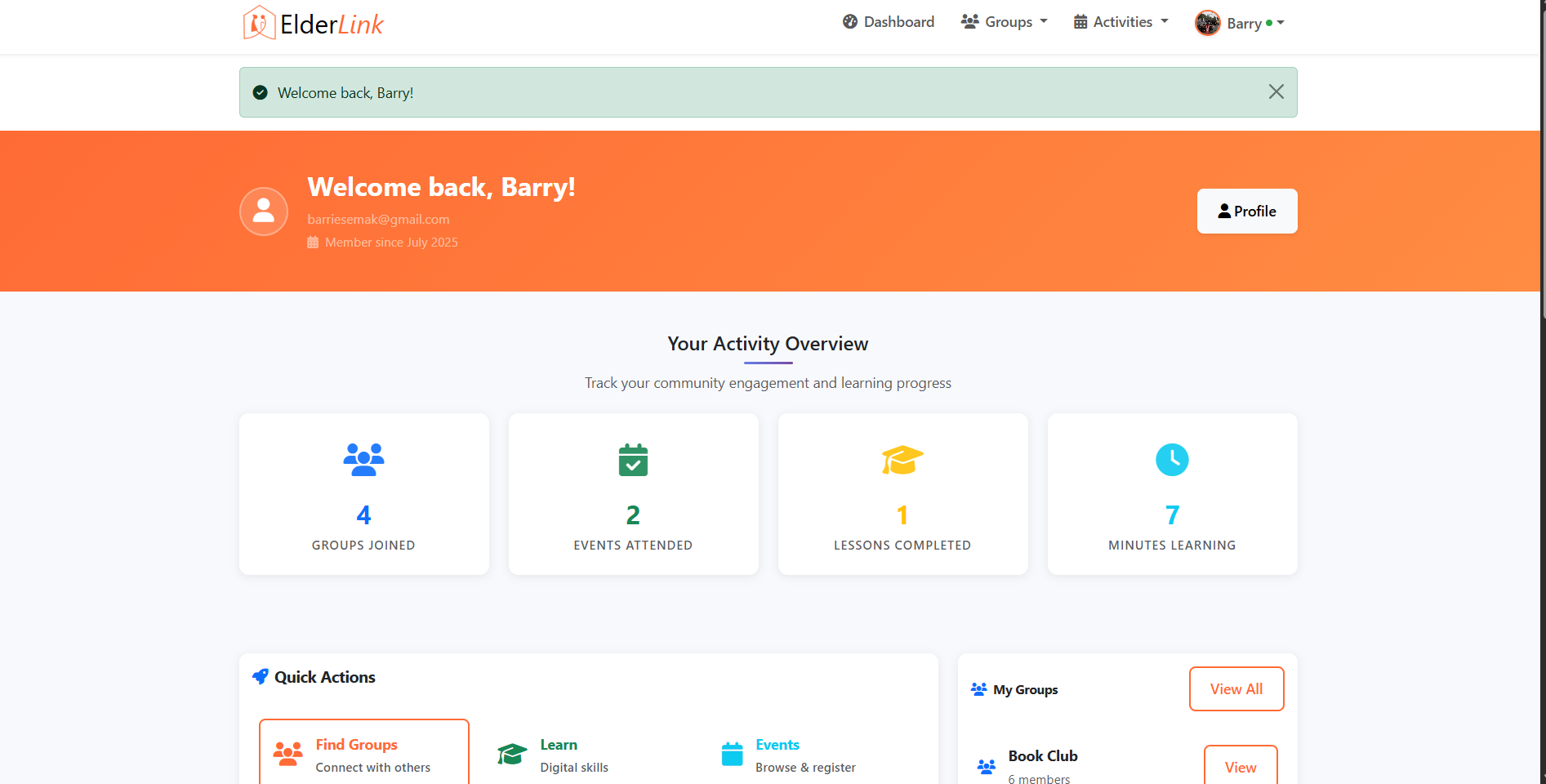
User Dashboard Access
Role-based dashboard view with permissions tailored to standard user access levels
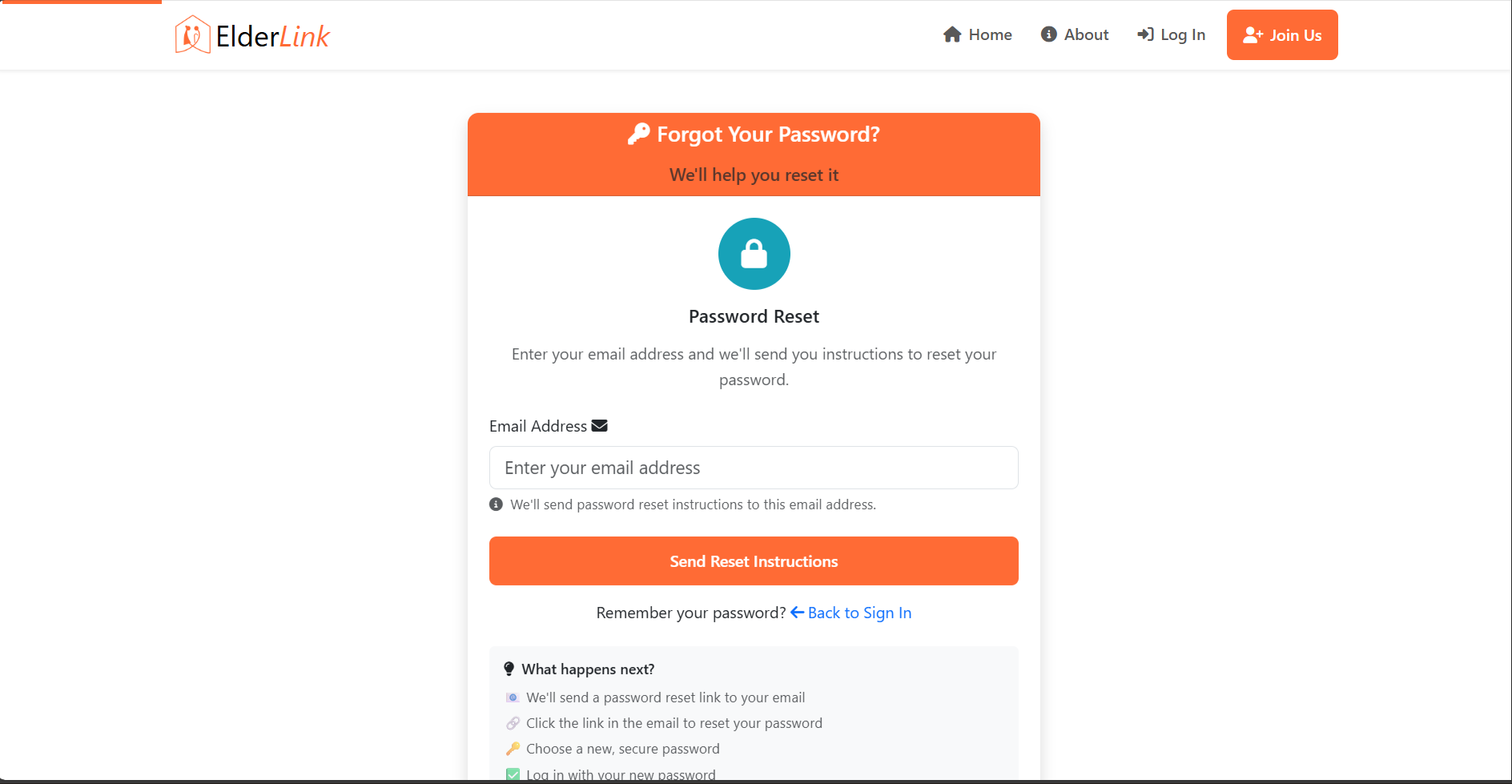
Password Reset Request
User-friendly password recovery interface with email-based reset link generation
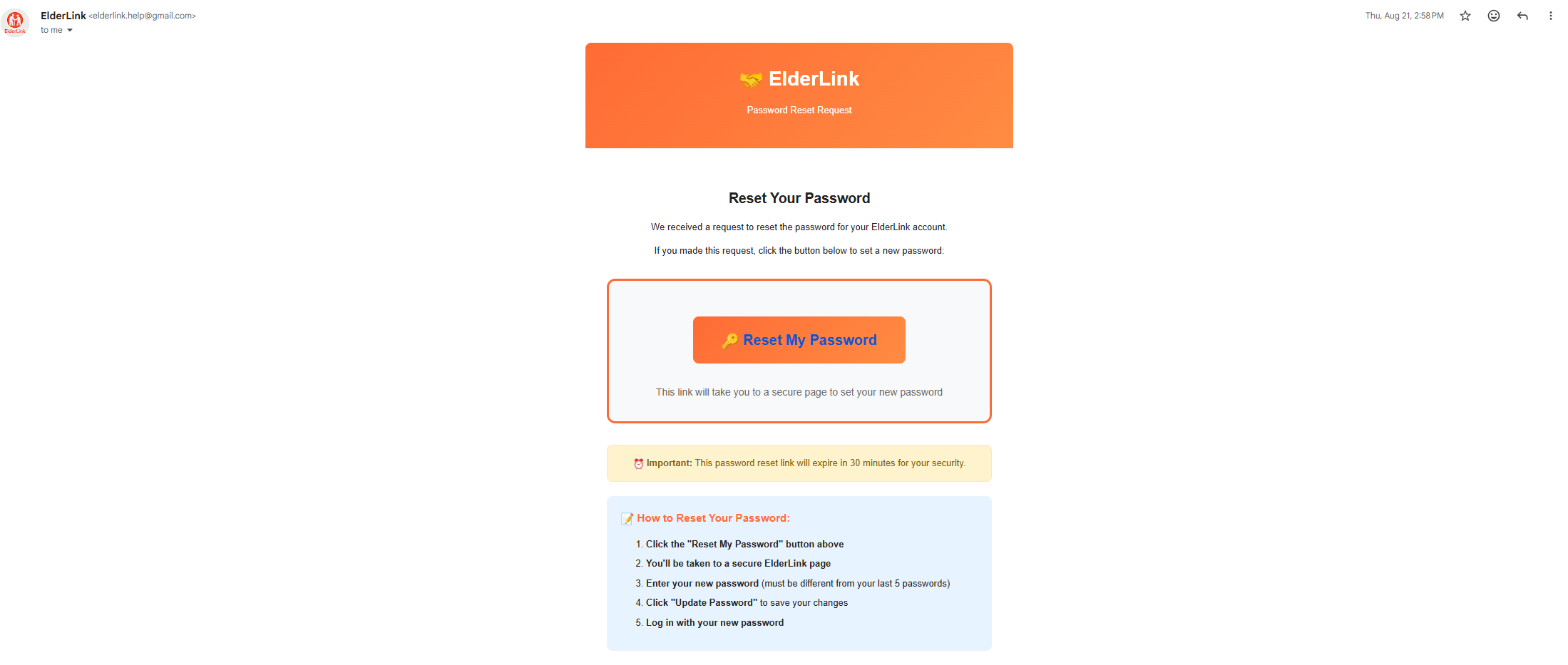
Secure Password Reset Email
Time-limited reset tokens (30-minute expiry) sent via SMTP with cryptographically secure generation
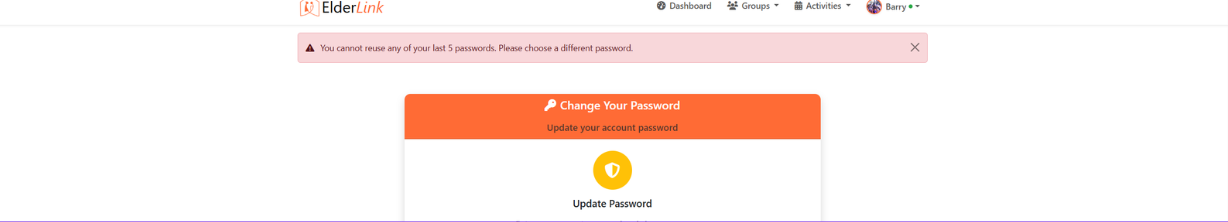
Password Change Security
Secure password update process requiring current password verification and strength validation
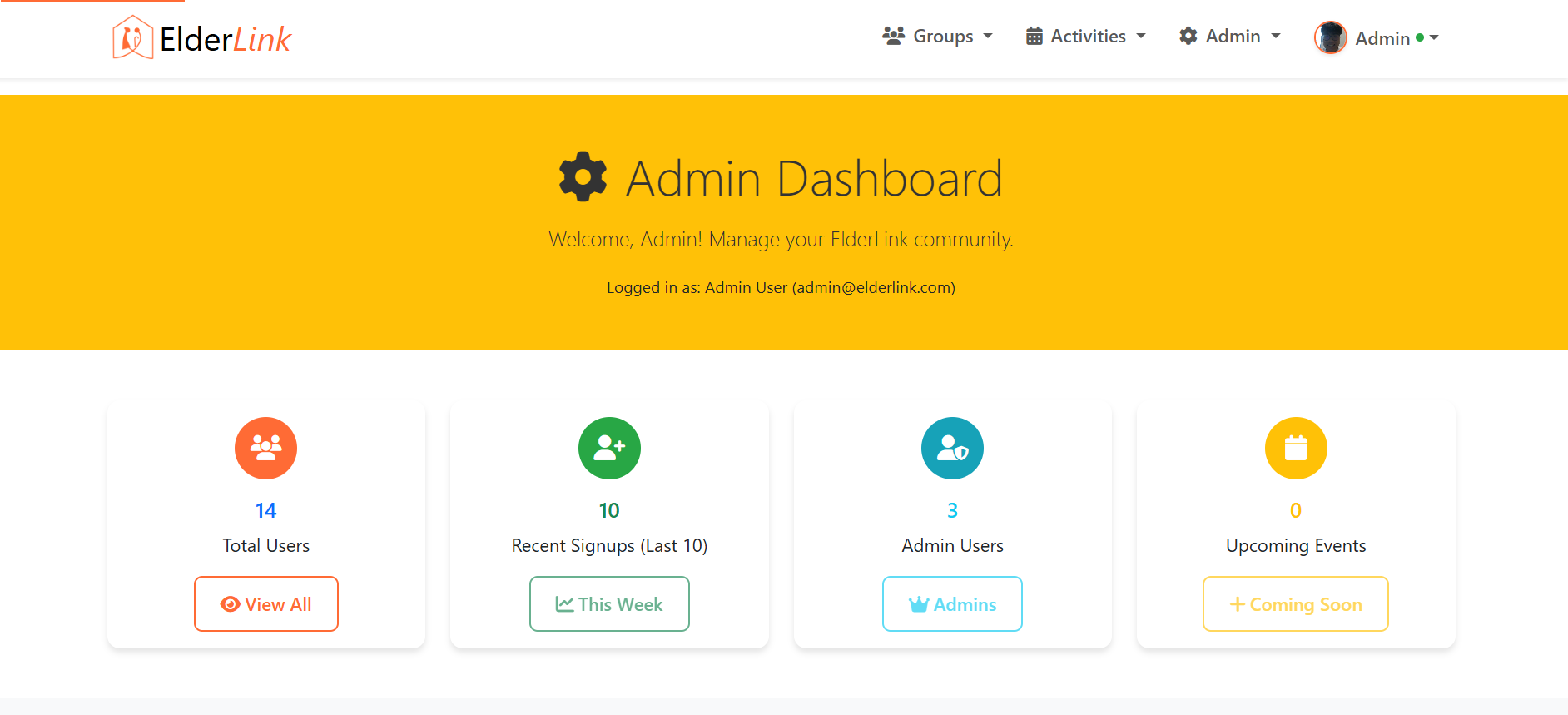
Admin Dashboard - Overview
Comprehensive admin interface with elevated permissions for platform management and monitoring
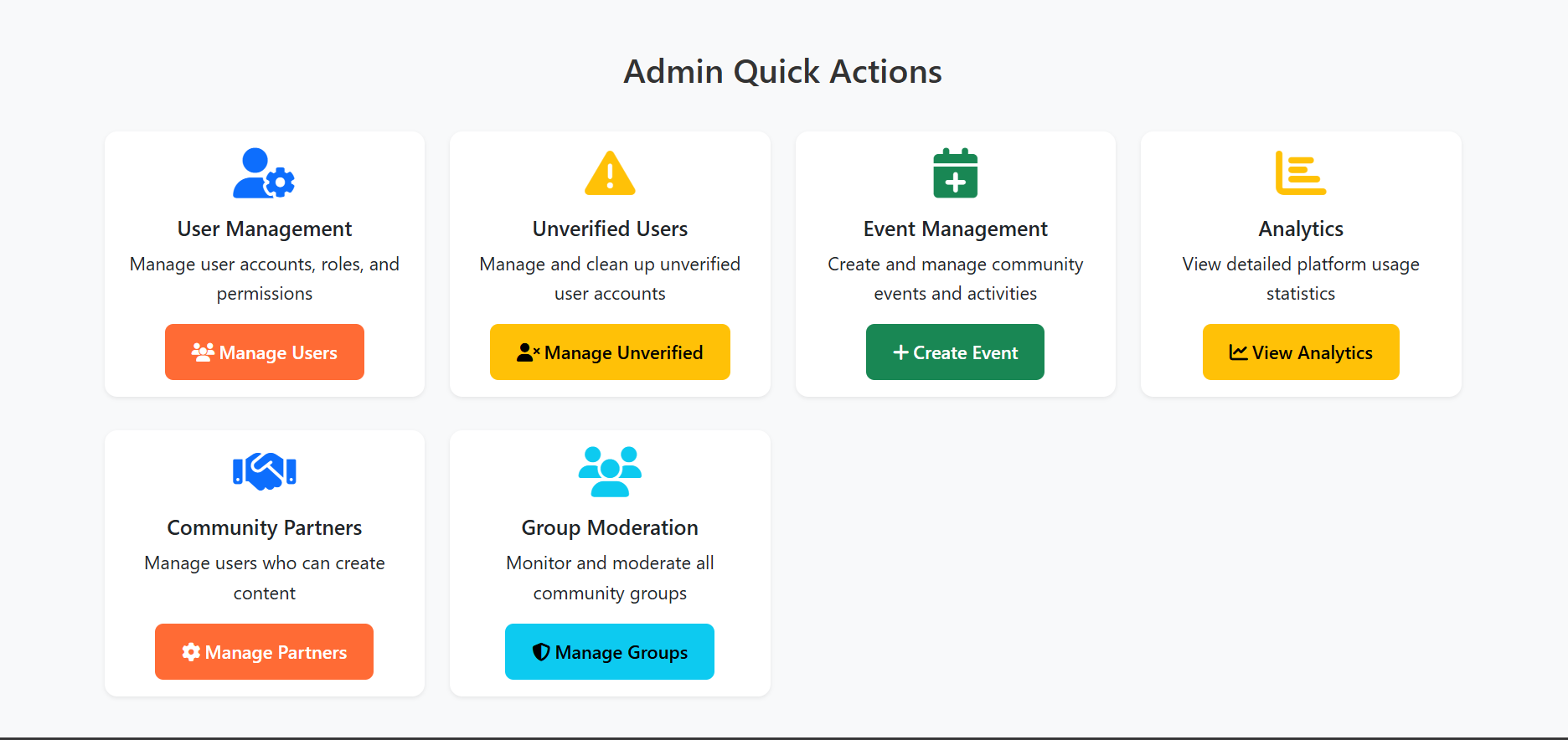
Admin Dashboard - Controls
Advanced administrative controls for user management, content moderation, and system configuration
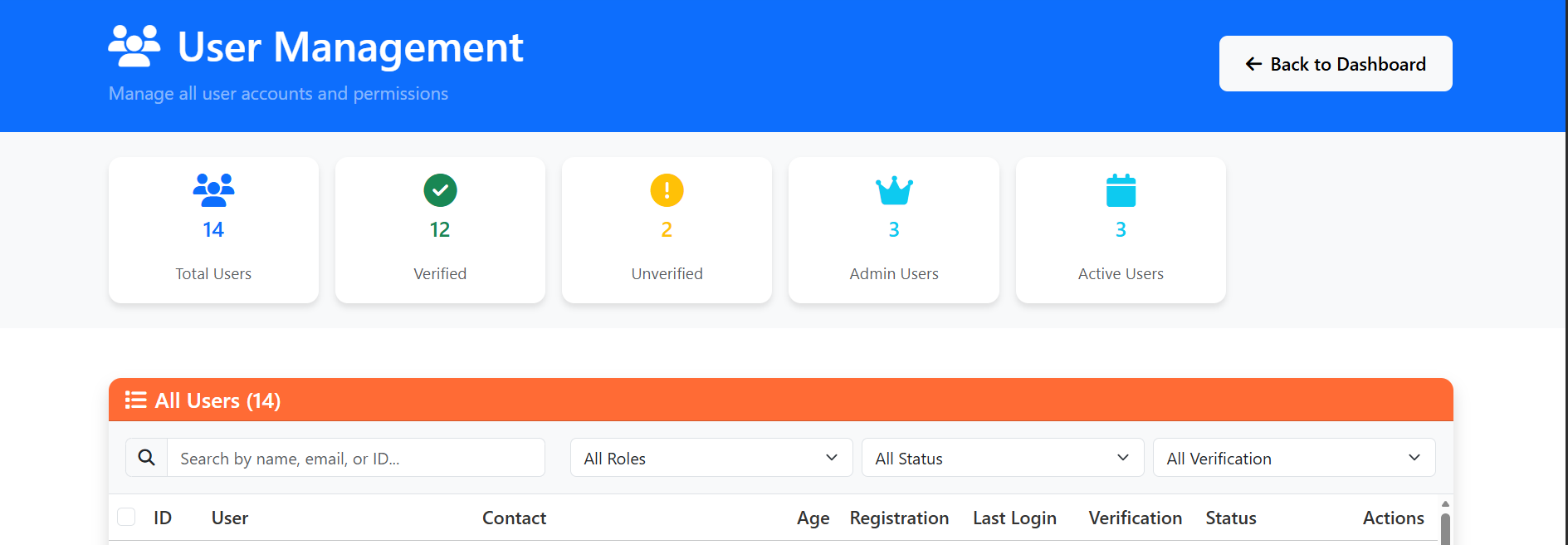
User Management System
Role-Based Access Control (RBAC) interface for managing user roles, permissions, and account status
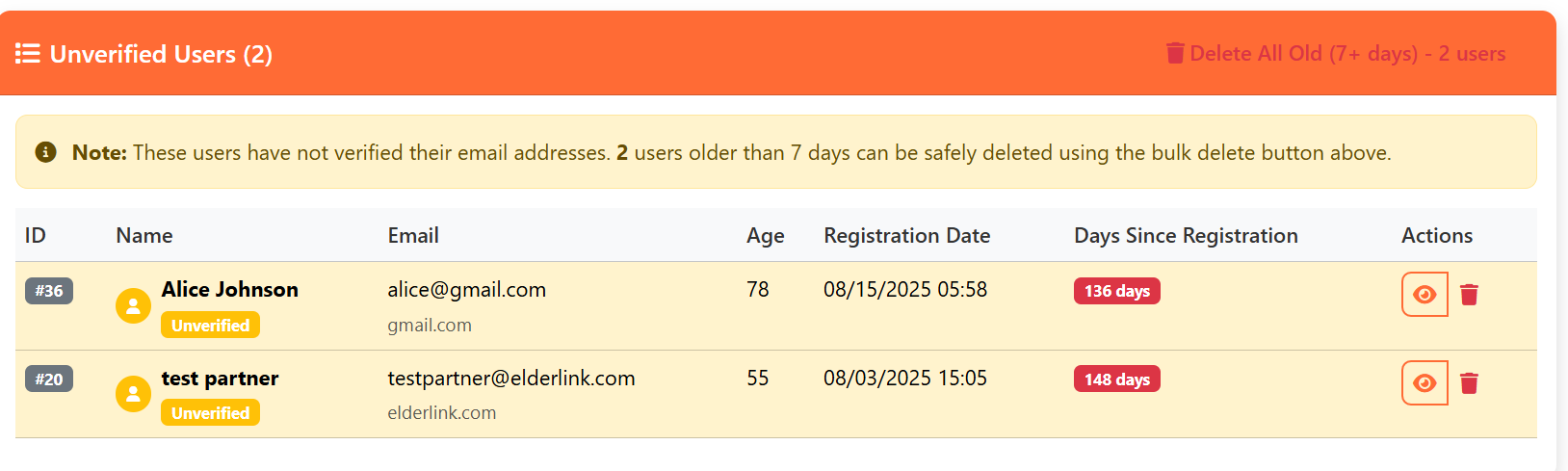
Unverified User Protection
Access control preventing unverified accounts from accessing platform features until email confirmation
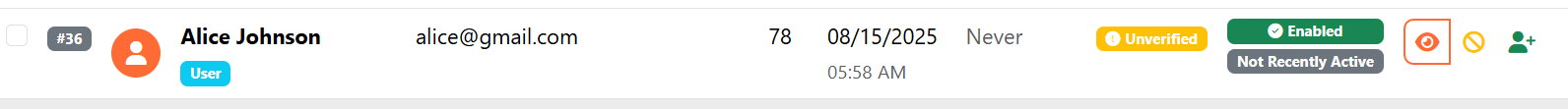
Account Suspension Control
Administrative capability to disable user accounts for policy violations or security concerns
Security Analytics - Metrics
Real-time monitoring of authentication events, failed attempts, and security metrics for threat detection
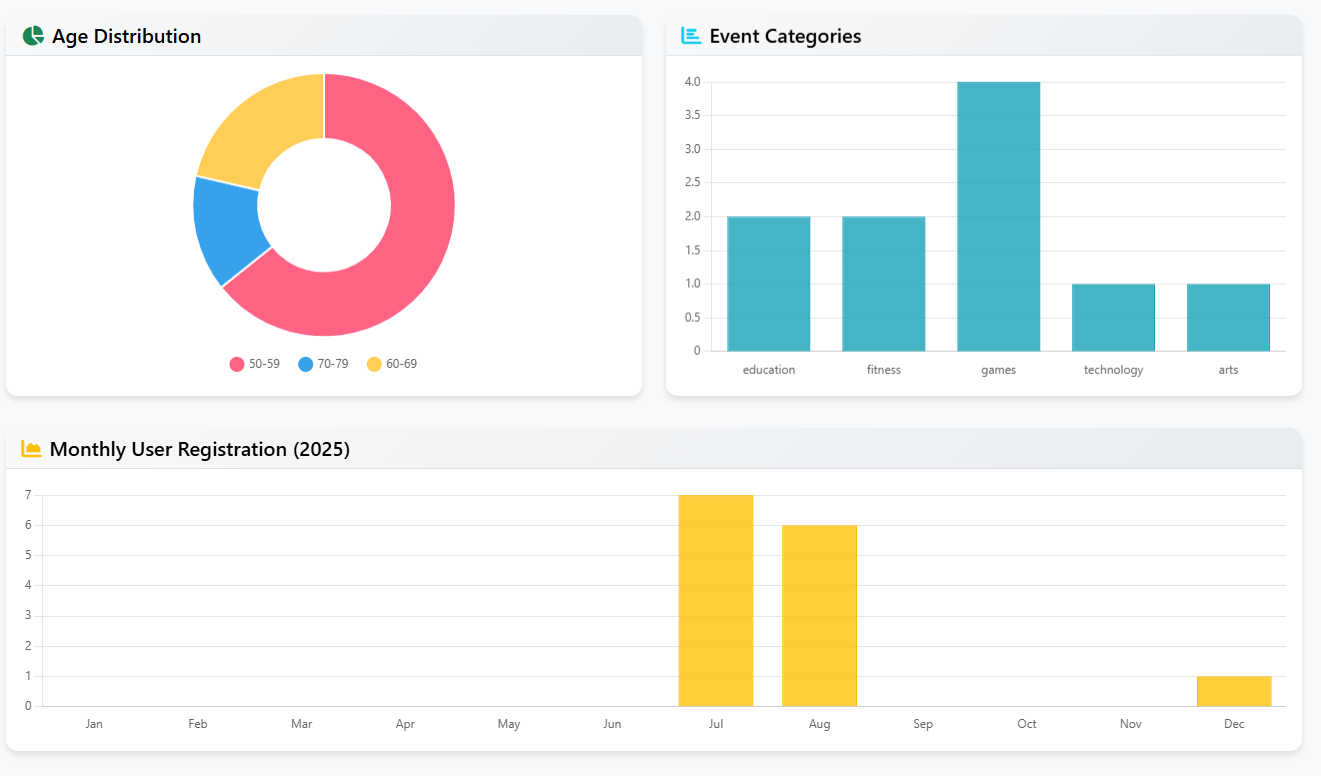
Security Analytics - Insights
Detailed security insights and user activity patterns for proactive threat identification and response