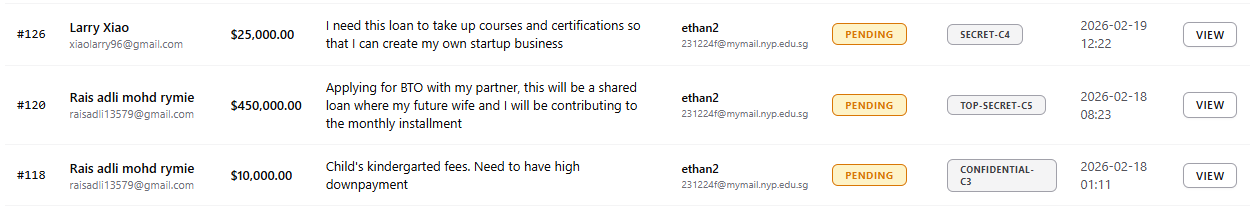
Features in Action
End-to-end walkthrough of the DigiLoan platform — from application submission to officer decision and email notification
Click image to enlarge
DigiLoan Homepage
The main landing page of the DigiLoan platform — providing applicants with a clean entry point into the loan application workflow, with navigation to begin the multi-step loan wizard
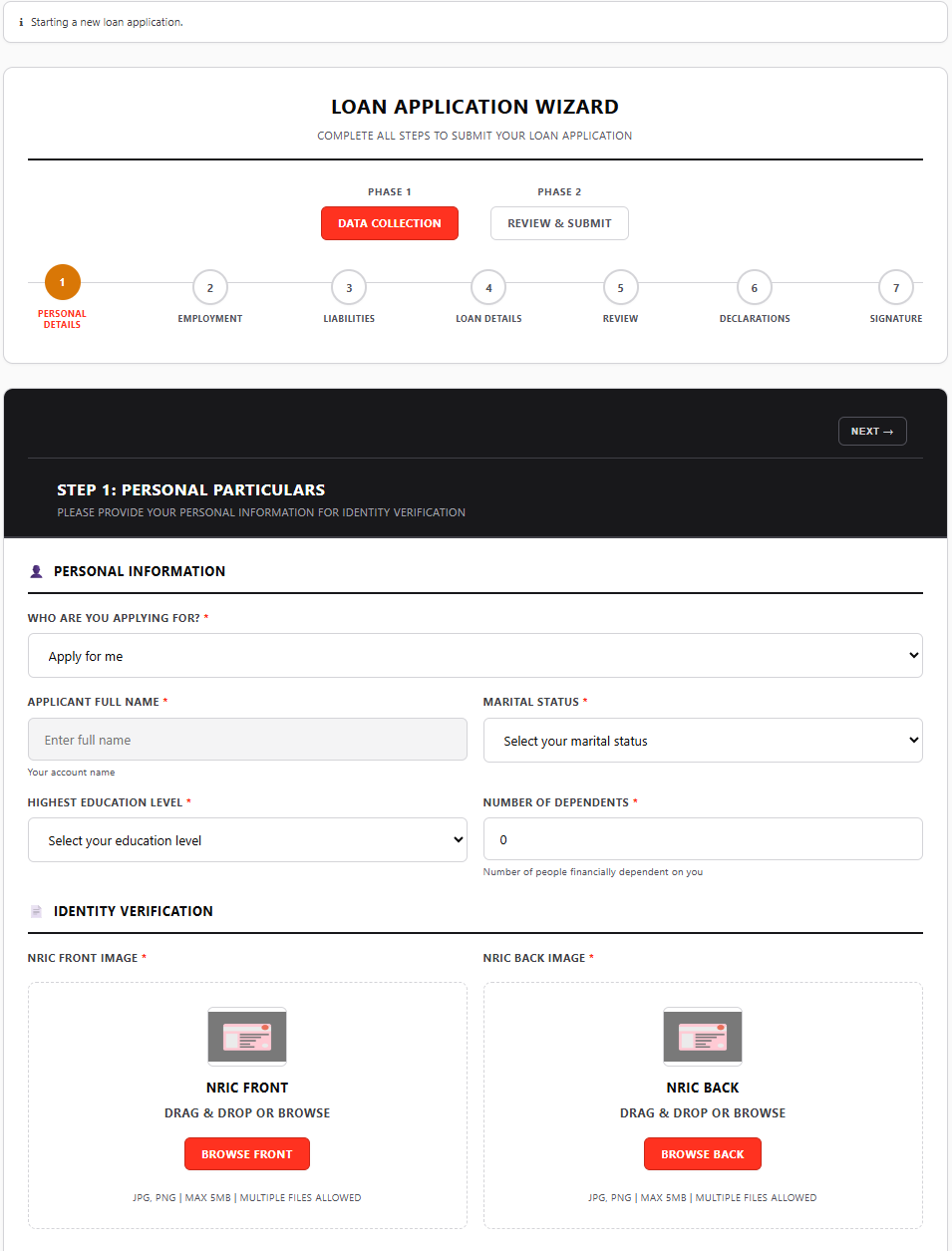
Multi-Step Loan Application Wizard
Guided multi-step form collecting personal details, employment information, loan amount, and supporting documents — with server-side validation at each step and CSRF protection on all POST operations
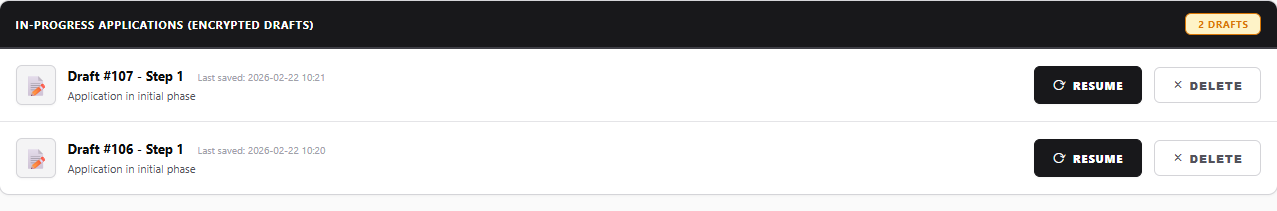
Encrypted Draft Saving
Applicants can save incomplete applications as drafts. Draft data is encrypted using Fernet (AES-128-CBC + HMAC-SHA256) at the field level — ensuring sensitive form data is protected even during mid-application pauses
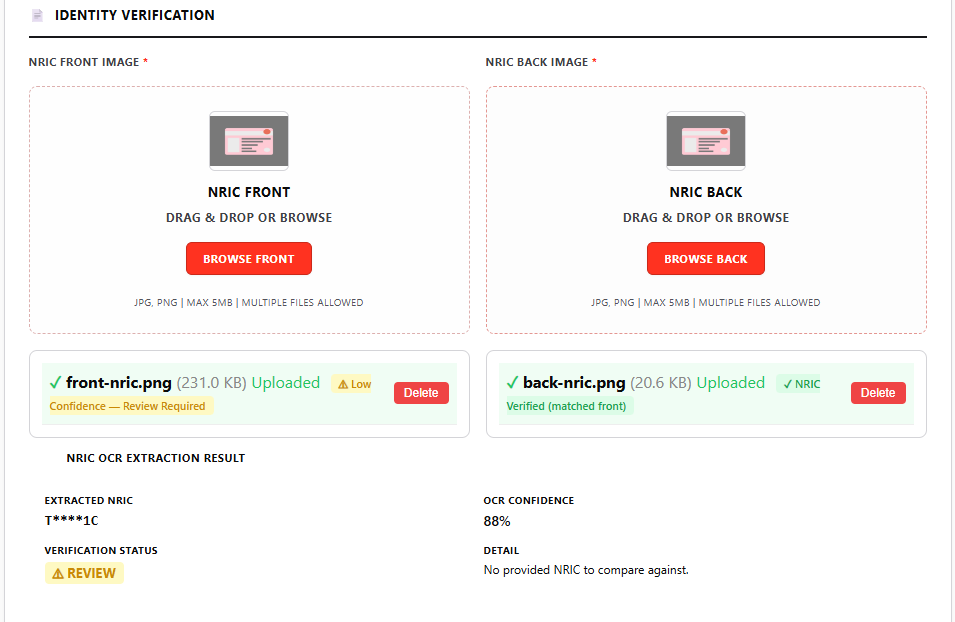
NRIC Identity Verification via OCR
Applicants upload their NRIC card image — the EasyOCR + OpenCV pipeline preprocesses the image, extracts the NRIC using three strategies, validates via MOD-11 checksum, and stores only the SHA-256 hash. Plaintext is deleted in-memory immediately after use
Loan Submission Confirmation
Upon submission, the ADC Engine automatically classifies the application (C0–C6), the Stage 1 HMAC-SHA256 digital signature is generated, permanent fields are encrypted with AES-256-GCM, and the applicant receives a confirmation screen with their application reference
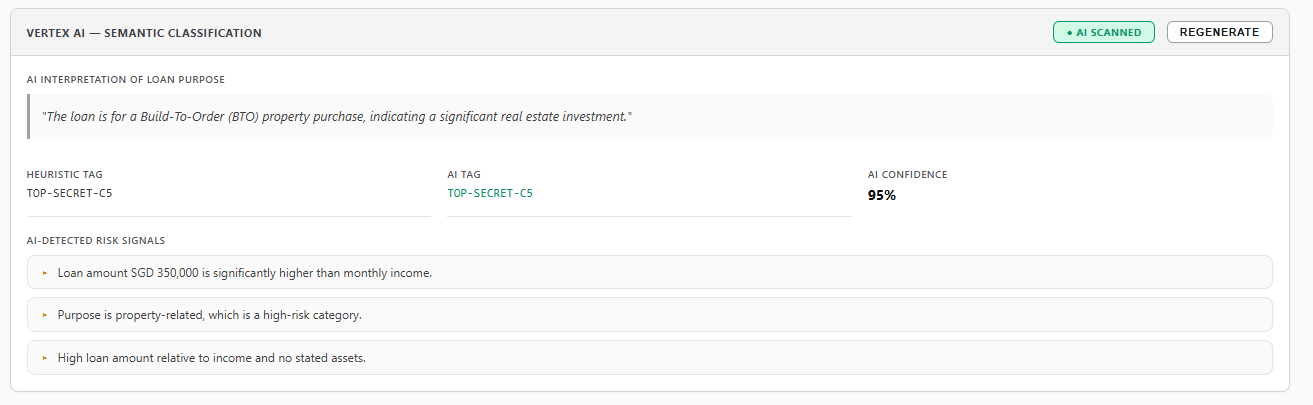
Vertex AI Semantic Classification
Phase 3 of the ADC Engine — Gemini 2.5 Flash Lite performs contextual semantic analysis of the loan application. Data minimization ensures NRIC and personal identifiers are stripped before leaving the server. The system uses a fail-open design: classification continues even if AI is unavailable
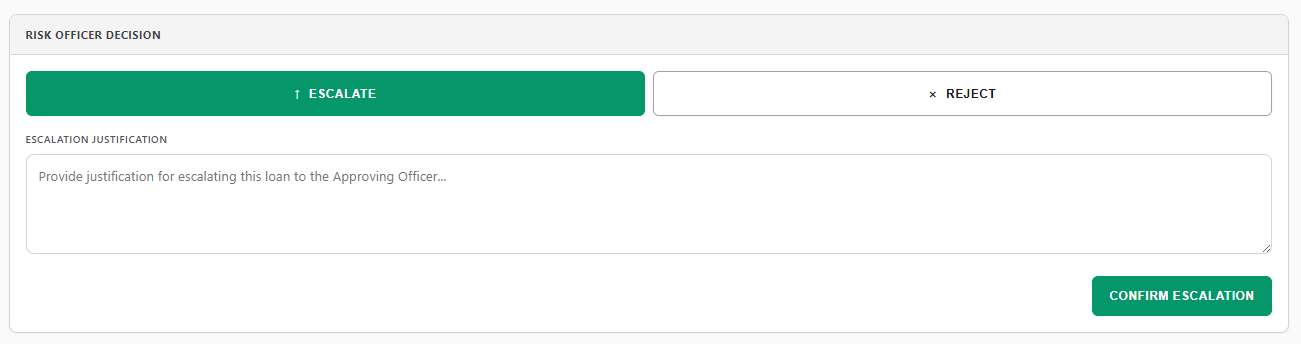
Reviewing Officer (RO) Escalation
The Reviewing Officer assesses the application and escalates to the Approving Officer with a justification. This action triggers Stage 2 of the digital signature system — an HMAC-SHA256 signature binding the officer ID, loan ID, justification text, and timestamp for non-repudiation
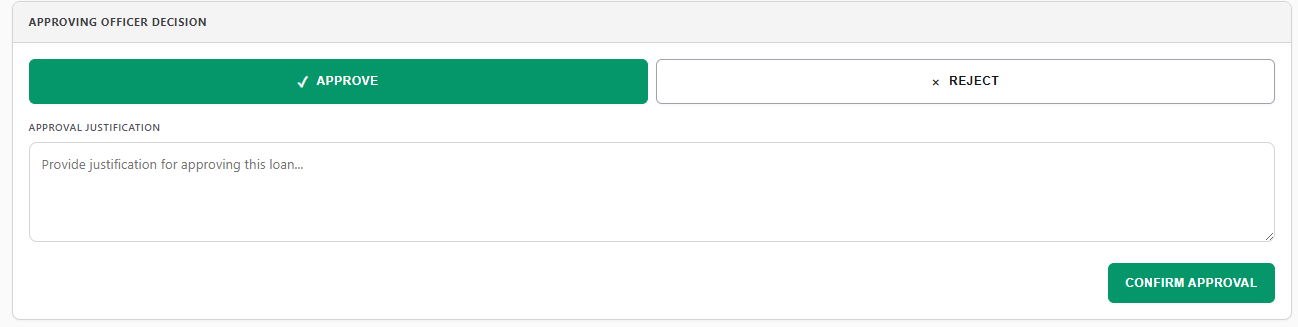
Approving Officer (AO) Decision
The Approving Officer makes the final approve or reject decision. Step-up re-authentication is required for C3+ classified loans. Stage 3 of the HMAC-SHA256 digital signature is generated — binding the officer ID, decision, loan ID, and timestamp — completing the non-repudiation chain
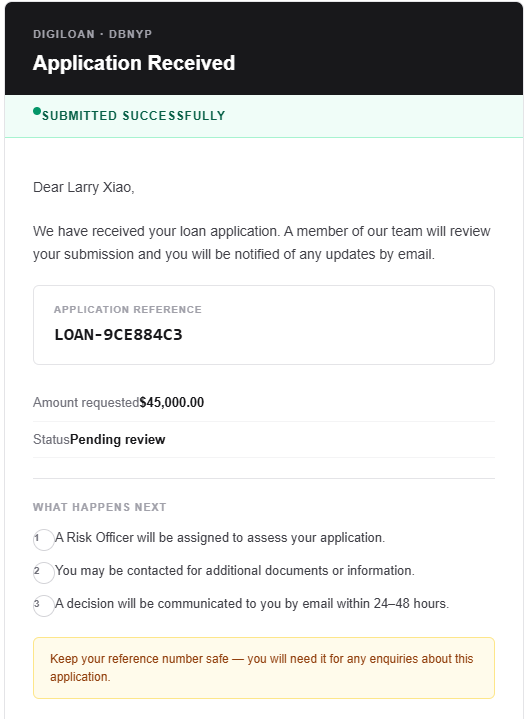
Application Received Email
Applicants receive an automated email confirming their loan application has been received and is under review. Delivered via SMTP with enforced TLS 1.2+ and certificate verification, with every delivery event audit-logged
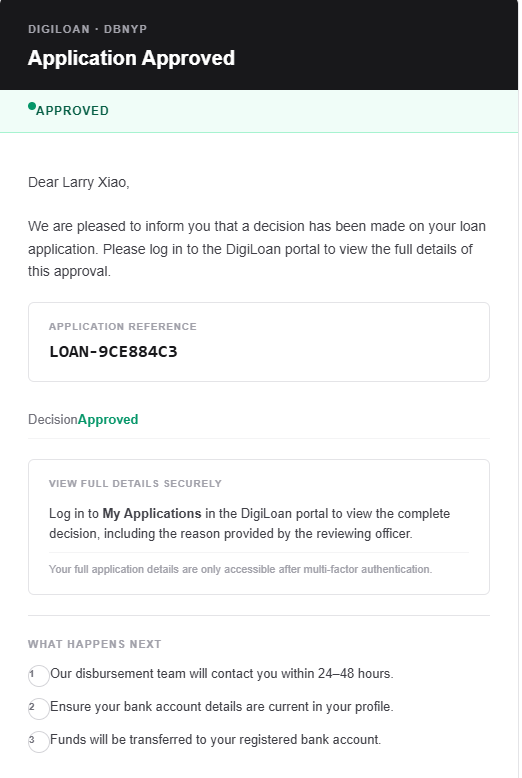
Loan Decision Email Notification
Upon AO decision, applicants automatically receive an approval or rejection email — completing the end-to-end loan workflow. The notification service enforces TLS 1.2+, verifies certificates, and logs all delivery events to the audit trail